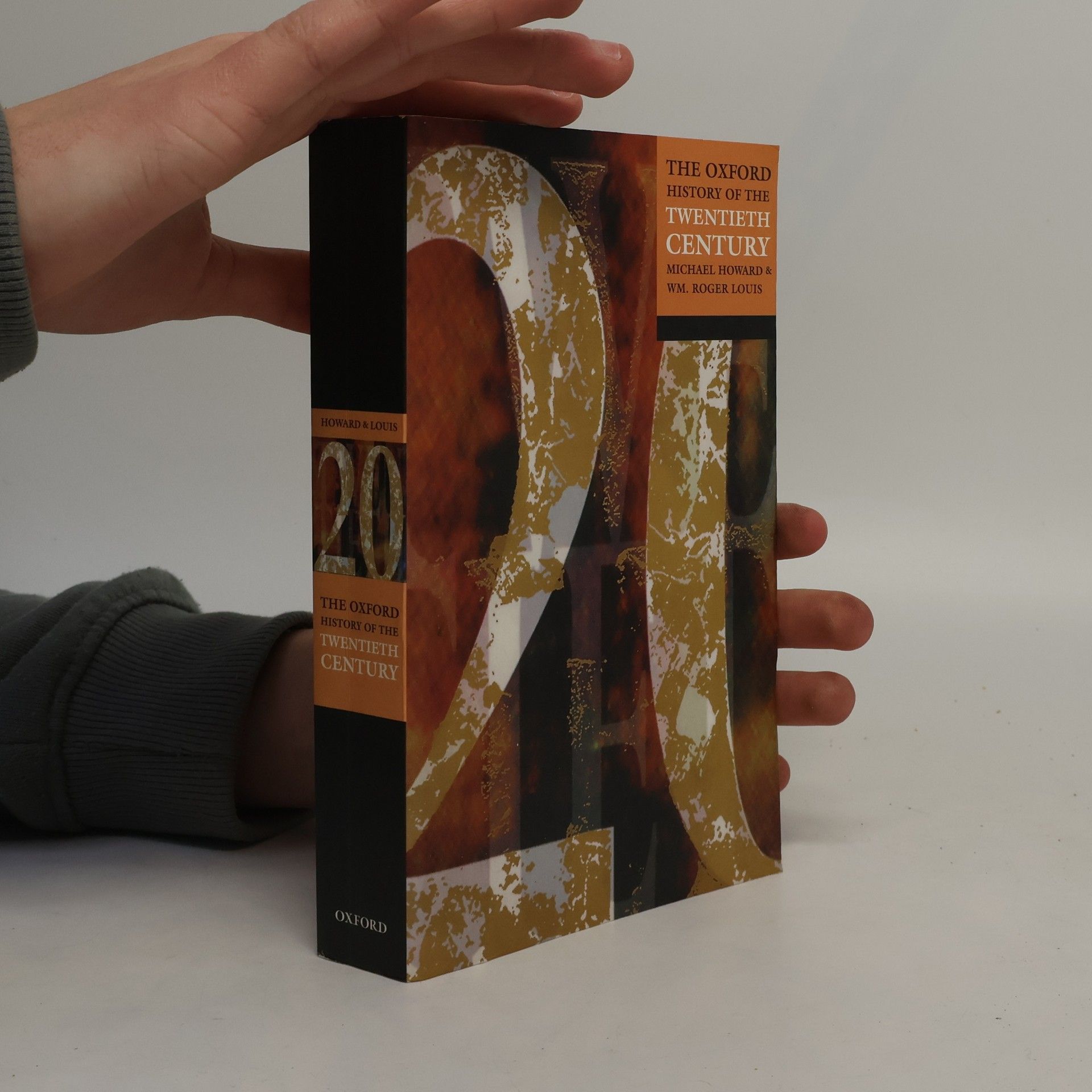
The Oxford History of the Twentieth Century
- 480 pages
- 17 hours of reading
The twentieth century stands out in history for its unprecedented change and transformation. Beginning in 1900, it was a time when Queen Victoria ruled England, the Imperial Manchu dynasty governed China, and the Romanov Tsars held sway in Russia. The era witnessed the nascent stages of cinema, with radio and television yet to be invented, and early automobiles on the roads while air travel remained a dream. This ambitious work features essays by twenty-four distinguished scholars who explore the significant events and themes of the century. They address political issues regionally and delve into non-political topics like physics, modern art, international economics, and the cultural impact of new technologies. The contributors examine enduring continuities and the transformative changes that defined the century. Initial chapters provide a global overview from various perspectives—demographic, scientific, economic, and cultural—while subsequent sections analyze the century's evolution continent by continent and region by region, all authored by recognized experts. Enhanced with color and black-and-white illustrations, a detailed chronology, further reading suggestions, and a comprehensive index, this work serves as an invaluable resource for understanding the complexities of the twentieth century.